How I Accidentally Joined Bug Hunting and Hacked Almost All Smart Speakers
A repair engineer obtains a blocked Yandex Station Mini and, out of curiosity, ends up discovering root access vulnerabilities across nearly the entire Yandex smart device lineup. The journey goes from soldering an SD card to the Wi-Fi module all the way to a formal bug bounty payout.
This story started with a simple repair job and ended with me participating in Yandex's bug hunting program. I'll be honest: I had no intention of becoming a security researcher. I just got my hands on a broken Yandex Station Mini and couldn't resist poking around.
The Starting Point: A Blocked Device
I run a small electronics repair shop. Someone brought in a Yandex Station Mini that had been blocked — Yandex locks devices when a subscription lapses or the account is deleted. The device itself works fine, but it refuses to do anything useful. I figured I'd take a look inside and see what could be done.
The hardware turned out to be fairly standard: an Amlogic A113x processor with Trust Security support, and a NAND flash chip (TC58NVG1S3HTA00). The UART interface was present but in silent mode, with an RH challenge/response authentication layer on top of it. Not a trivial crack.
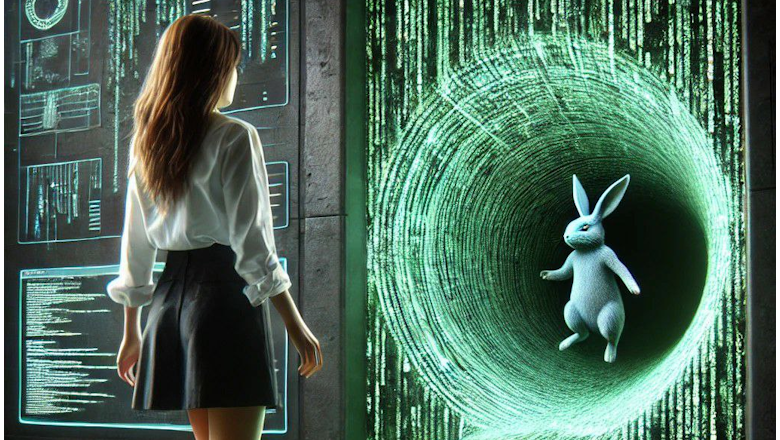
Finding the Rabbit Hole
I dumped the firmware from the NAND and started going through the filesystem. In /etc/init.d/S01enable_sh I found a startup script with a curious reference: rabbit_hole_debug. An Alice in Wonderland reference, clearly. The script logic was simple: if the environment variable rabbit_hole_debug equals 1, spawn a shell on the UART port.
So there's a backdoor, right there in the startup scripts. The question was how to set that environment variable without already having access to the device.
The SD Card Trick
After some research I found a way in. The Amlogic bootloader supports an aml_autoscript on an SD card — a script that runs during boot before the main OS. I soldered an SD card directly to the SDIO interface, parallel to the Wi-Fi module (they share the same bus on this board).
The plan:
- Create an
aml_autoscriptthat setsrabbit_hole_debug=1in the U-Boot environment - Intentionally corrupt the data partition to force the device into recovery mode
- Recovery mode reads U-Boot env variables — including my newly set one
- The startup script sees the variable and spawns a shell
It worked. I had root.
The Subscription Bypass
With root access, I could see everything. The device configuration contained parameters directly controlling subscription status — flags that told the device whether it was in a valid, paid state. Modifying them locally was straightforward. The device would boot up and act as if it had an active subscription.
However, that only got me so far. Yandex's Alice voice assistant communicates with backend servers through a service called uniproxy. On every connection, the server verifies the device's status independently. So even with locally patched config files, the moment Alice tried to contact the server, the block was re-enforced. Local bypass: successful. Full bypass: blocked by server-side validation.
Scaling Up: The Yandex Station Max
After documenting everything, I decided to look at the bigger siblings. The Yandex Station Max uses a more powerful SoC but a similar software stack. The same rabbit_hole_debug pattern was present. I reported this to Yandex's bug hunting program and received compensation — the Max qualified as a valid target under their scope.
The Devices Yandex Didn't Want to Hear About
I also looked at the Yandex Duo and Yandex TV Pro. Both showed similar architectural patterns and the same style of startup script backdoors. I submitted these findings as well. Yandex's response was that these devices fell outside their bug bounty scope and the vulnerabilities would not be recognized as security issues. Make of that what you will.
What This Means in Practice
The core finding is that the debug backdoor — a feature almost certainly inserted during development to make testing easier — was never removed from production firmware. The rabbit_hole_debug variable is a textbook example of a development artifact that shipped to millions of end users.
For a blocked device that you own, this is arguably useful knowledge. For a device in someone else's home, gaining root access this way would be illegal regardless of the technical elegance of the method.
I want to be clear: this research was self-directed, done on hardware I owned, and motivated purely by curiosity and the technical challenge. I have no affiliation with any hacking group. The bug bounty submission was the responsible path once I understood the scope of what I'd found.
A follow-up post covering the Yandex Station Max in more technical detail is planned.



