Browser Fingerprinting Has Become a Mass Phenomenon
Browser fingerprinting has evolved from a niche security concern into widespread commercial use by advertisers, with 2025 research providing the first concrete evidence of mass deployment across the top 10,000 websites.
Introduction
Browser fingerprinting -- a technique for uniquely identifying users even without cookies or JavaScript -- has evolved from a niche security concern to widespread commercial deployment by advertisers. What was once a theoretical privacy threat is now a mainstream tracking technology.
Historical Context
The technique first gained public attention in 2019, when Google AdSense banners were caught executing fingerprinting scripts. The script sca.17.4.95.js was discovered collecting dozens of browser characteristics to create unique "portraits" of devices. The banner attempted to use the Audio API alongside dozens of other data points.
How Fingerprinting Works
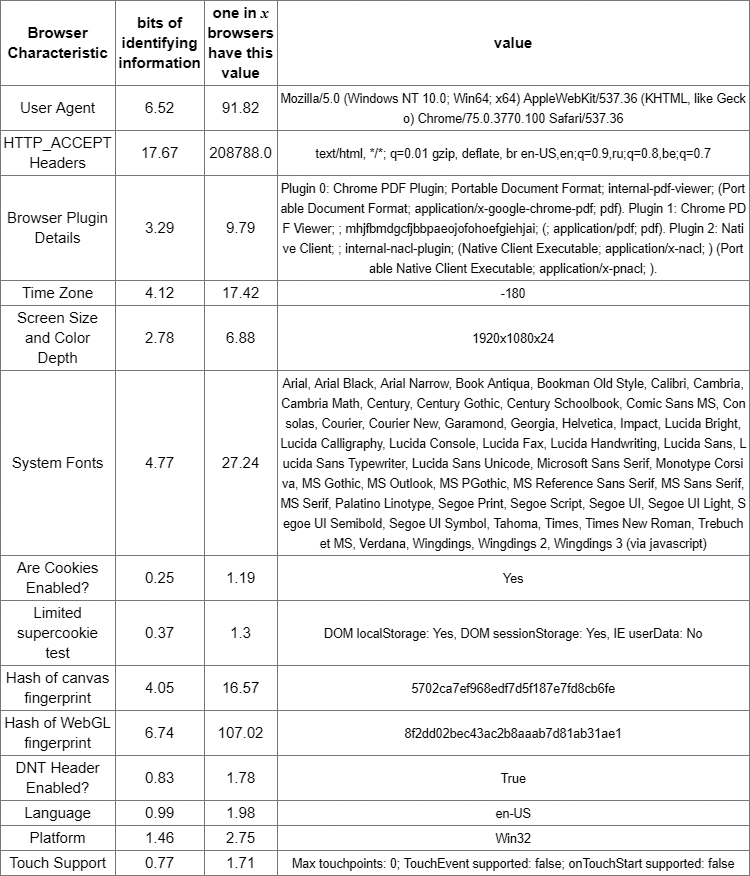
The fingerprinting process gathers multiple data points to create a unique identifier for each browser instance. The data collection methods include:
- Display resolution and accessibility parameters via media queries
- Installed fonts on the system -- the specific combination of fonts is surprisingly unique
- Cryptographic API availability -- which crypto functions the browser supports
- Audio API capabilities -- how the browser processes audio reveals hardware and software details
- Mobile-specific APIs -- accelerometer, gyroscope, and other sensor data
- DRM support for specific platforms -- which content protection systems are available
The Panopticlick Experiment
The Electronic Frontier Foundation operates Panopticlick (now Cover Your Tracks), a tool that demonstrates just how unique browser fingerprints are. In testing, a browser showed "17.67 bits of identifying information" among 208,788 tested users over a 45-day period. This means the browser was effectively unique among over 200,000 users -- without using a single cookie.
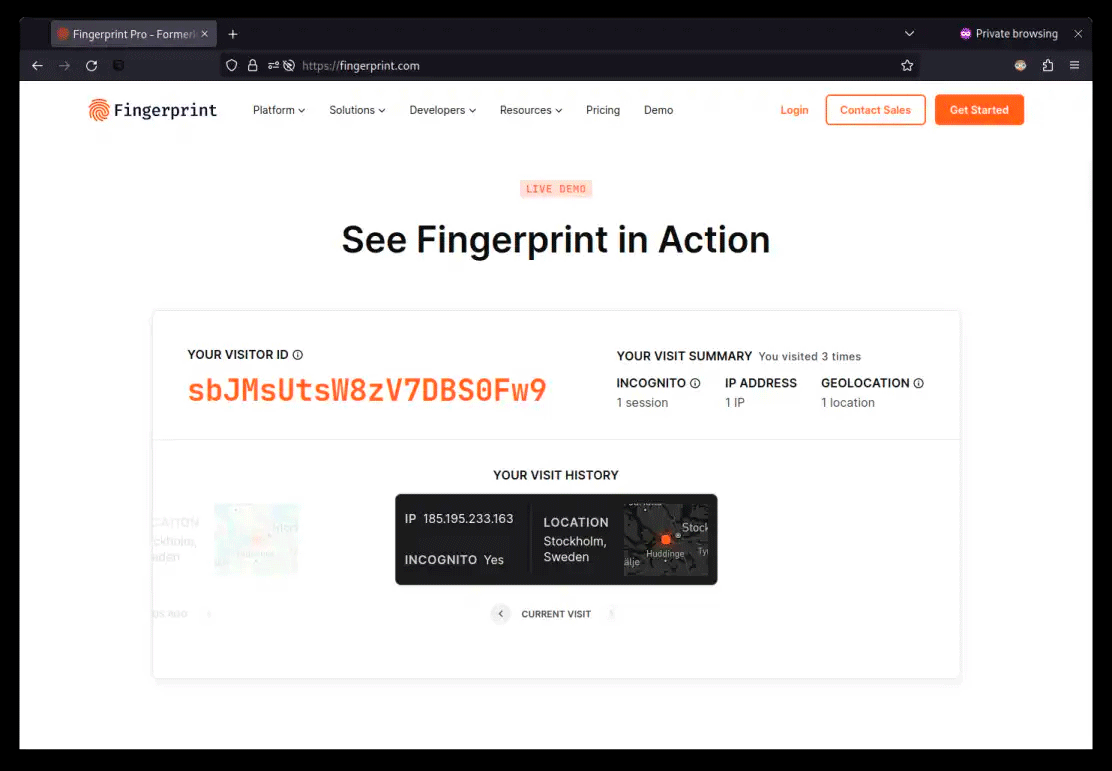
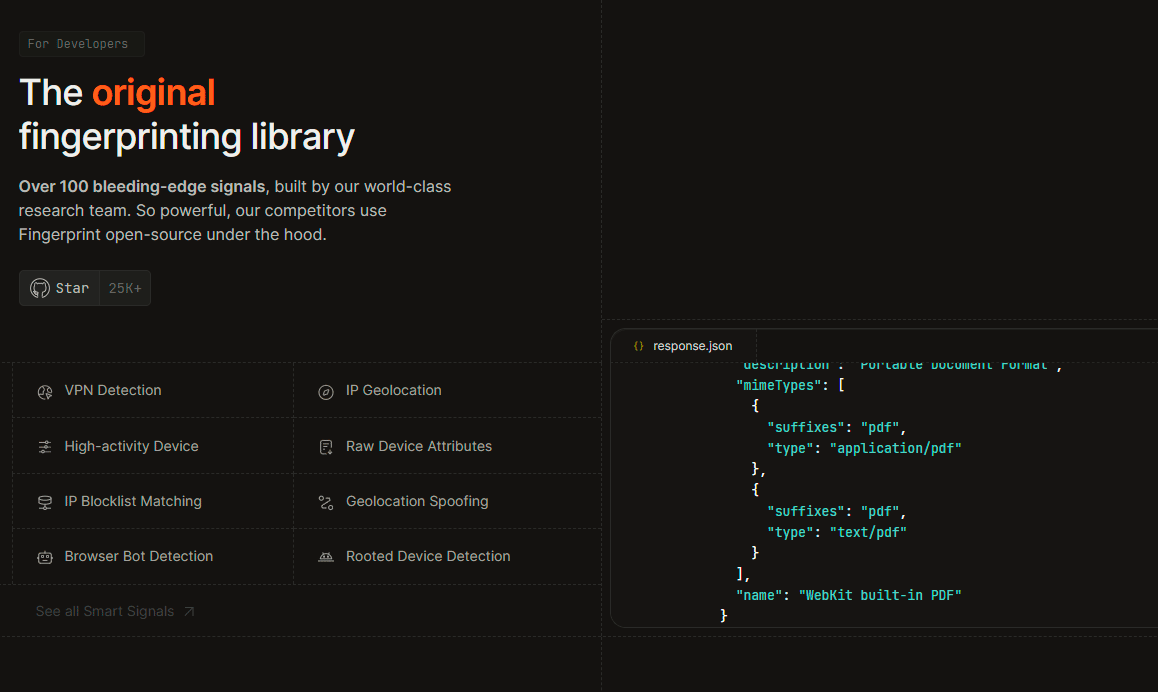
Commercial Adoption
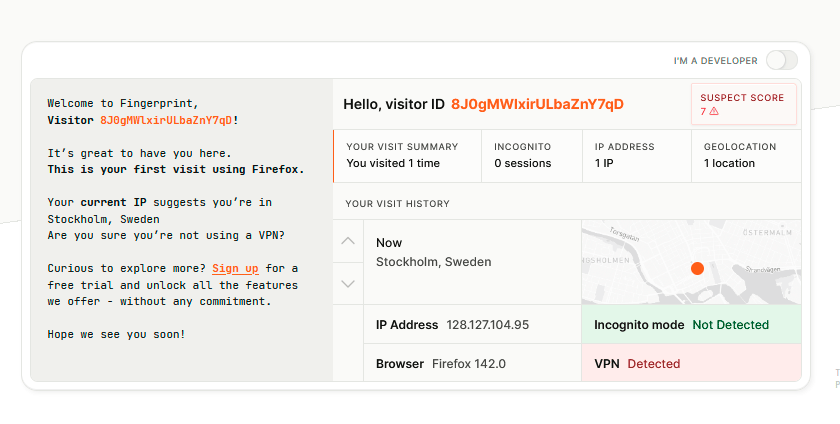
Fingerprinting has spread far more widely than most users realize. Specialized SaaS services now offer fingerprinting as a commercial product, complete with APIs, SDKs, and technical support. These services make it trivial for any website operator to implement sophisticated user tracking without traditional cookies or identifiers.
2025 Research Findings
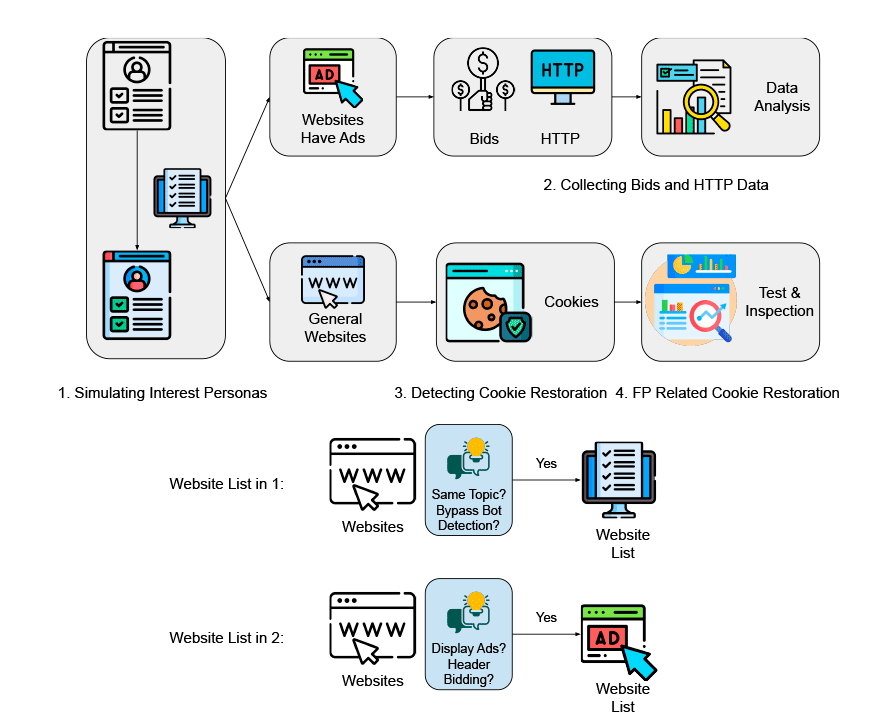
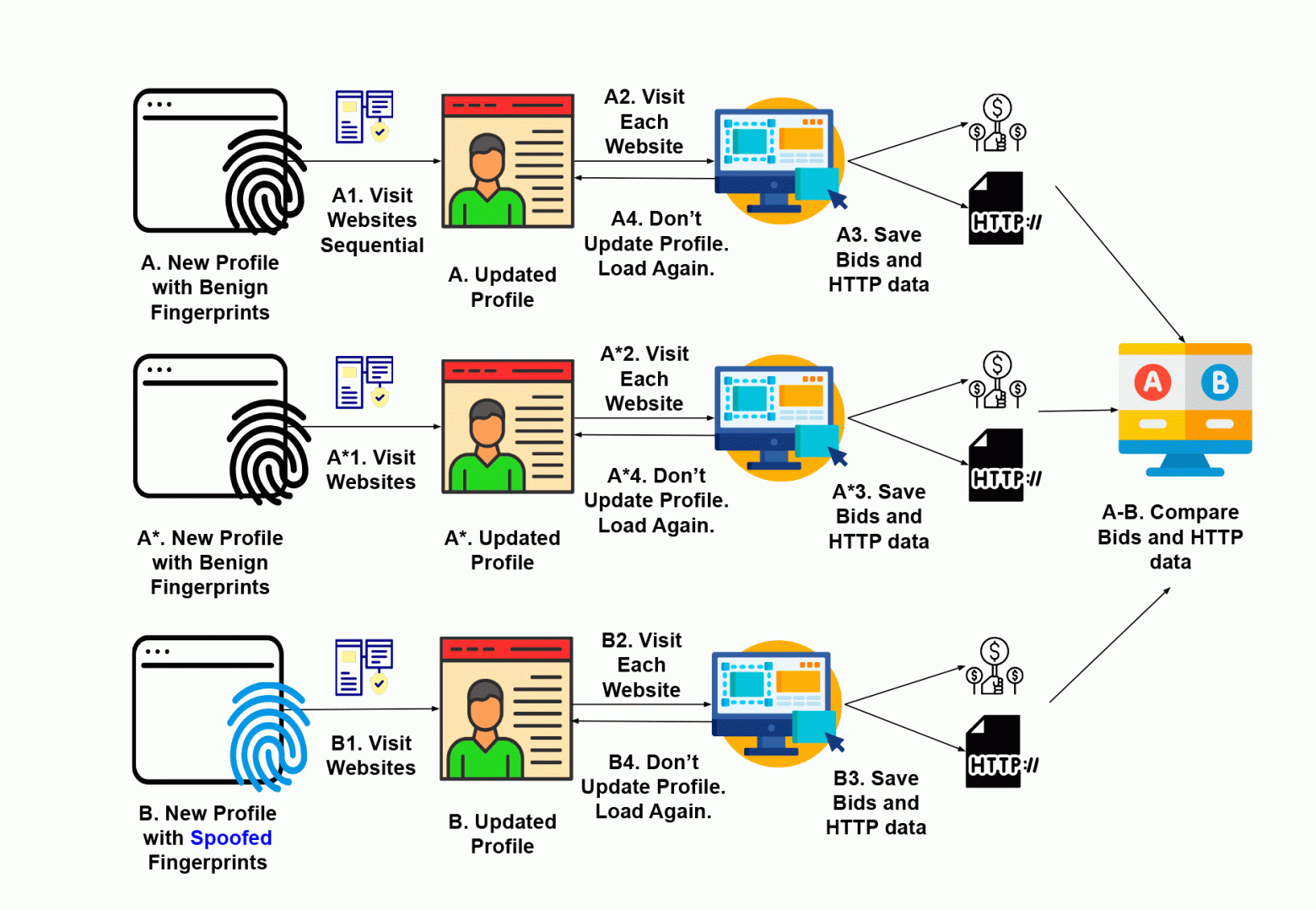
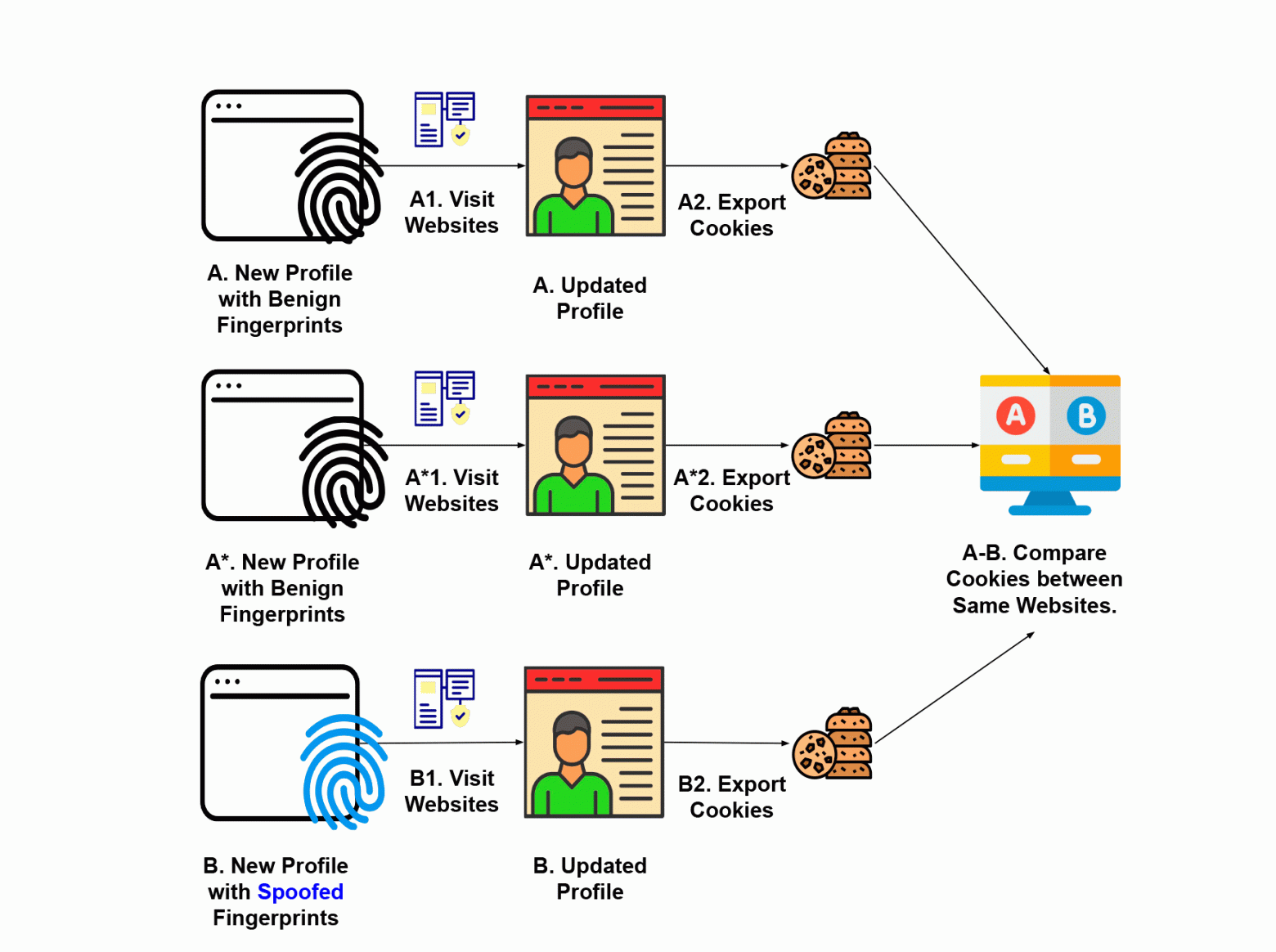
A groundbreaking 2025 scientific study evaluated the prevalence of internet-wide fingerprinting through the FPTrace framework. The researchers examined the Alexa Top 10,000 websites using a rigorous methodology:
- A/B testing -- comparing behavior with different browser fingerprints
- Data leak analysis -- monitoring what data is transmitted to third parties
- Browser profile manipulation -- testing how sites react to changed fingerprints
- Advertising price comparisons -- checking if fingerprint data affects ad pricing
The results demonstrated that browser fingerprints substantially influence ad targeting and HTTP traffic patterns between servers and clients. According to researcher Dr. Nitesh Saxena: "Fingerprinting always raised privacy concerns, but we lacked convincing evidence of actual tracking deployment."
This research provides the first concrete evidence of mass application of fingerprinting in the advertising industry, raising serious privacy concerns about a tracking method that most users cannot detect or prevent.
Privacy Protection
While complete protection against fingerprinting is extremely difficult, some tools exist:
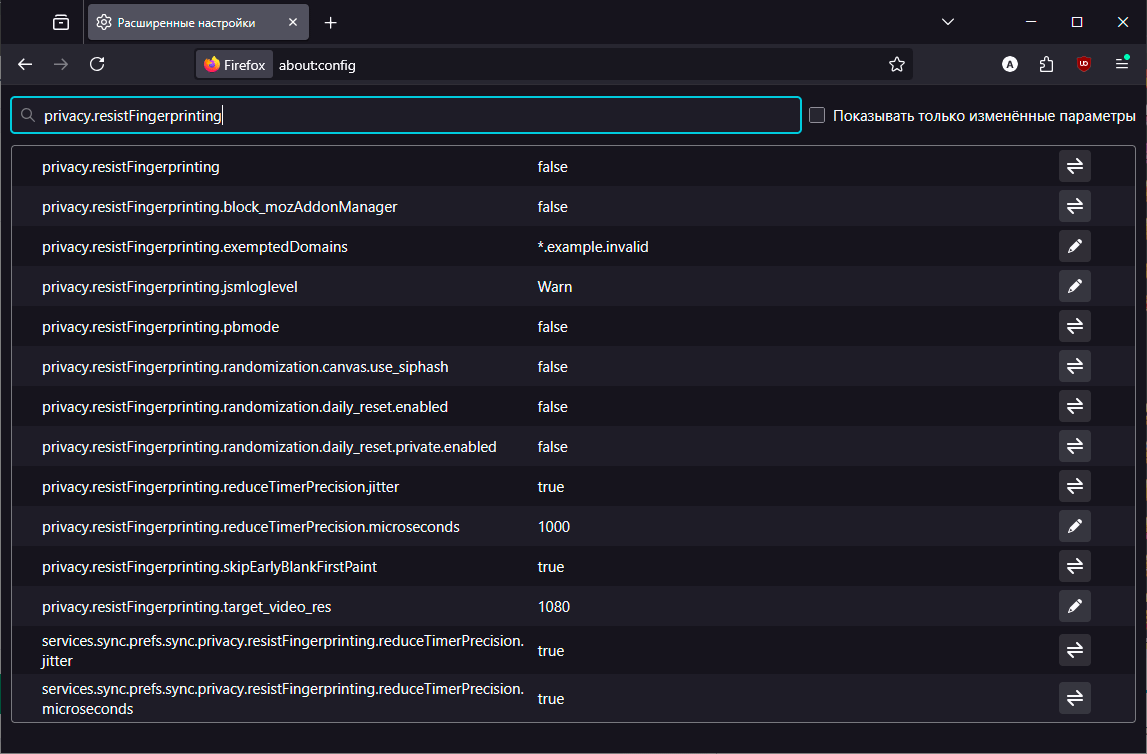
- Firefox offers built-in fingerprinting resistance through the
privacy.resistFingerprintingconfiguration setting, which normalizes many of the data points used for fingerprinting - Tor Browser is designed to make all users look identical, defeating fingerprinting by design
- Browser extensions can block known fingerprinting scripts, though this creates its own fingerprint
The Paradox of Protection
There is a fundamental paradox in fingerprinting protection: the very act of using anti-fingerprinting tools can make a user more identifiable, not less. If only 2% of users enable privacy.resistFingerprinting in Firefox, then having that setting enabled becomes itself a distinguishing characteristic. True protection requires widespread adoption of privacy tools so that many users share the same fingerprint.
Conclusion
Browser fingerprinting has crossed the threshold from theoretical threat to mainstream advertising technology. The 2025 research confirms what privacy advocates long suspected: fingerprinting is being actively used at scale across the web's most popular sites. As cookies face increasing restrictions from browser vendors and privacy regulations, fingerprinting is likely to become even more prevalent -- making it one of the most important privacy challenges of the coming decade.
FAQ
What is this article about in one sentence?
This article explains the core idea in practical terms and focuses on what you can apply in real work.
Who is this article for?
It is written for engineers, technical leaders, and curious readers who want a clear, implementation-focused explanation.
What should I read next?
Use the related articles below to continue with closely connected topics and concrete examples.





