I Will Find You and Call You: How Telecom Carriers Legally Sell Your Location and Call Metadata
An investigation revealing how telecom carriers legally sell website visit data, call metadata, and geolocation to marketing agencies — enabling stalking, fraud, and corporate espionage for pennies.
Completely legal tools for laughably small amounts of money can allow you to call all the active customers of your competitors, build a dozen effective fraud schemes, or even call the suspected lover of your girlfriend/wife — and while you're at it, check where she was last night! I discovered this during one of my investigations into client data leaks. And I firmly believe this should not exist. The tool used in this article is more effective than database breaches. Our data should not be so easily and legally traded in near real-time. You can find anyone — where they go, where they live and sleep — and call them. Why and how does this work, what risks does it carry, and how can we fight it? I'll explain below.
The Investigation That Started It All
In autumn, a large client came to me with a fairly typical problem — lead leakage from a website that collects applications. It worked like this:
- A customer submits an application on the website.
- That same day, the client's call center contacts them.
- The next day, malicious actors call and start selling their own product.
This affected a significant portion of customers, but not all of them. By the time the investigation began, the leak had been ongoing for more than a month. We worked through the standard hypotheses:
- Call center employees leaking data.
- A technical data leak from the website.
- Data leaked by partners and contractors.
- Targeting of the company's customers.
But this article is by no means PR for the investigation, and I won't bore you with the details of how we eliminated one theory after another. What matters is what we found.
Many people know how targeted advertising works, and mobile carriers openly sell data about website visits to marketing agencies.
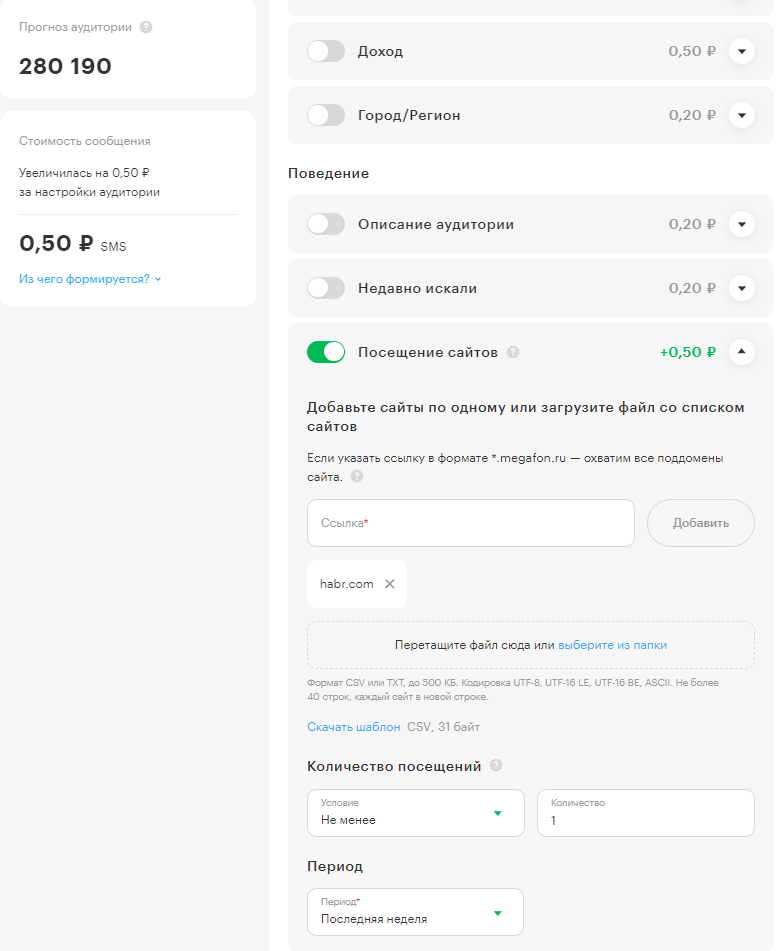
Here, for example, is an audience forecast from one of the mobile carriers for targeting everyone who visited Habr in the past week! Approximately 280,000 people, with the cost of an SMS to each running a few rubles plus 0.5 rubles for this additional filter. Yes, information about your website visit costs 50 kopecks.
How does it work? These are all website visits via mobile internet! The carrier can see the domain you're accessing — it's not encrypted by default in TLS.
Can you only buy from one carrier? No, they resell each other's services, so you can track subscribers from multiple carriers through a single carrier's dashboard. They distribute the profits from selling your data among themselves.
Website visit data has been traded for a long time, allowing SMS to be sent, and marketing agencies that buy this traffic can even CALL the victim — er, customer — though without transmitting the phone number. For paying for such a leak, you'll get a link through which you can call via an IP telephony gateway.
But this isn't as scary or effective, since lots of random people visit a website, leading to many junk calls from casual visitors. Our client was specifically losing submitted applications. They were only calling people who had submitted an application, and only those using mobile internet. But not everyone who visited the site.
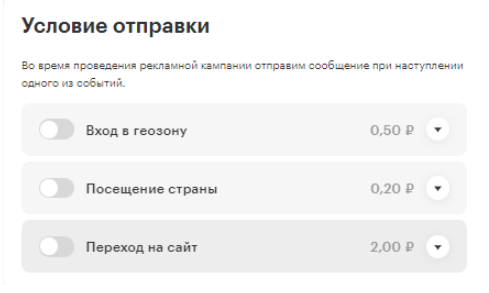
But not long ago, a new option appeared that allows tracking calls!
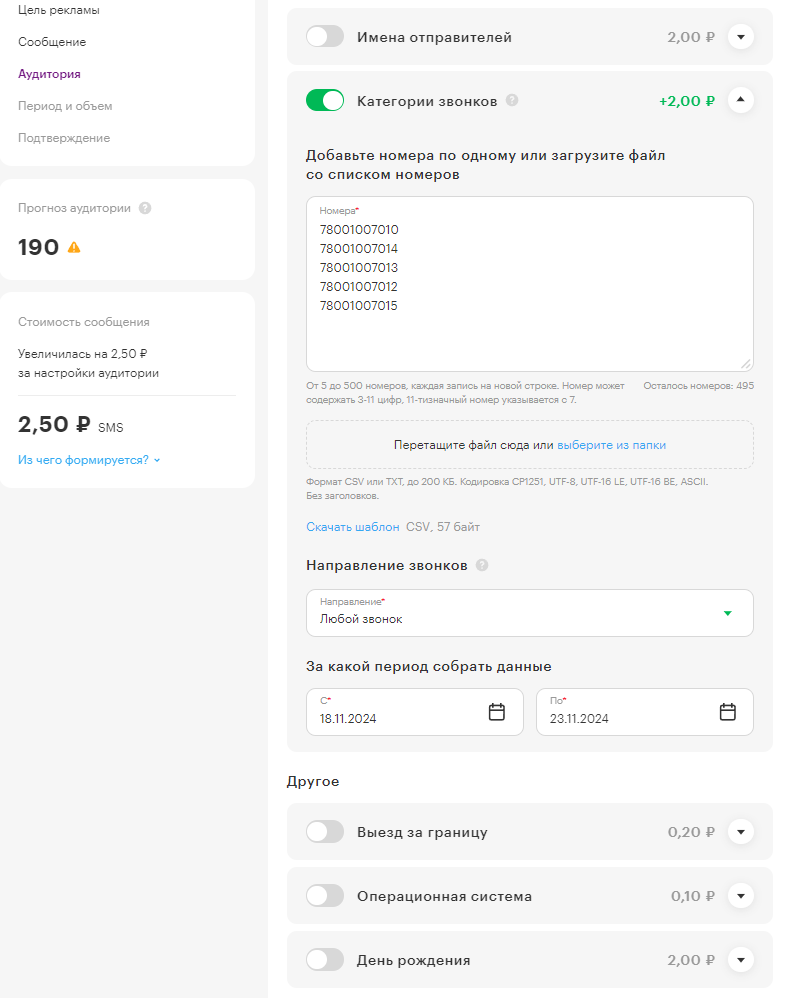
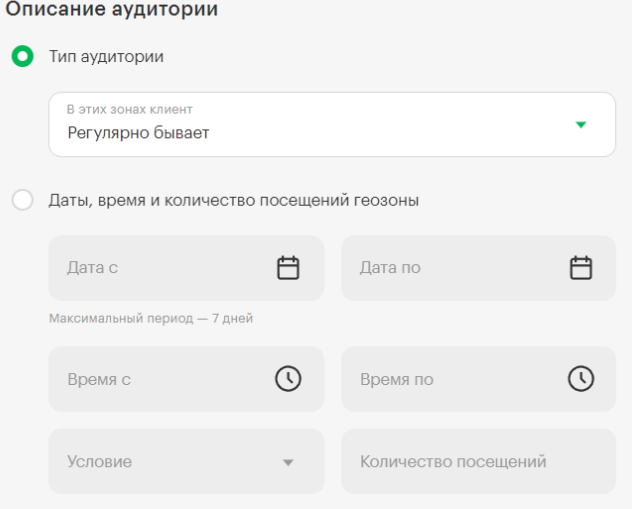
You're offered to enter at least 5 phone numbers and see how many of your victims — sorry, customers — have called those numbers. Or were called from those numbers, or as shown on the screenshot, "any direction." 190 people out of 280,000 Habr users in the past week communicated with Gosuslugi (Government Services) tech support, since their number is 78001007010.
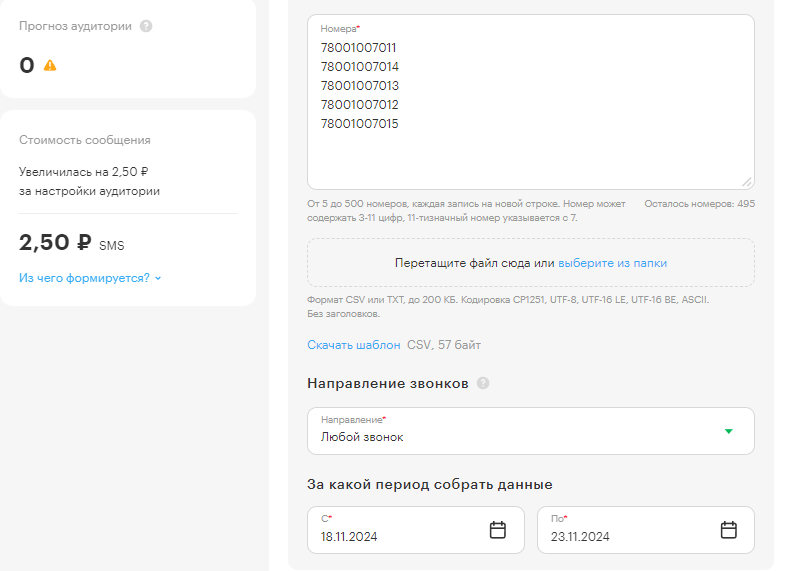
How am I sure it's exactly 190 and the other 4 numbers didn't contribute? They don't exist — you can enter any nonexistent numbers there. Here's proof: I changed the first number to another nonexistent one, changing the final 0 to 1, and the audience sample came back empty!
This is exactly how our client's leads were being stolen. The attackers set up filters for:
- Visit to the company's website.
- Call from the company's call center number.
The client's call center called all applicants, and the very next day this appeared in the marketers' dashboard, where for a small fee they could call everyone matching the filter!
Yes, leaking your phone call metadata costs just 2 rubles extra!
I'm attaching the full list of available filters and conditions:
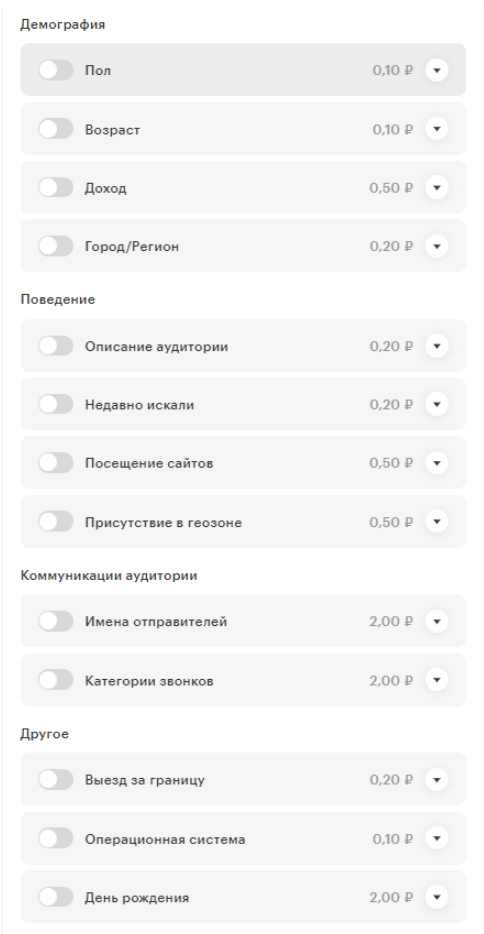
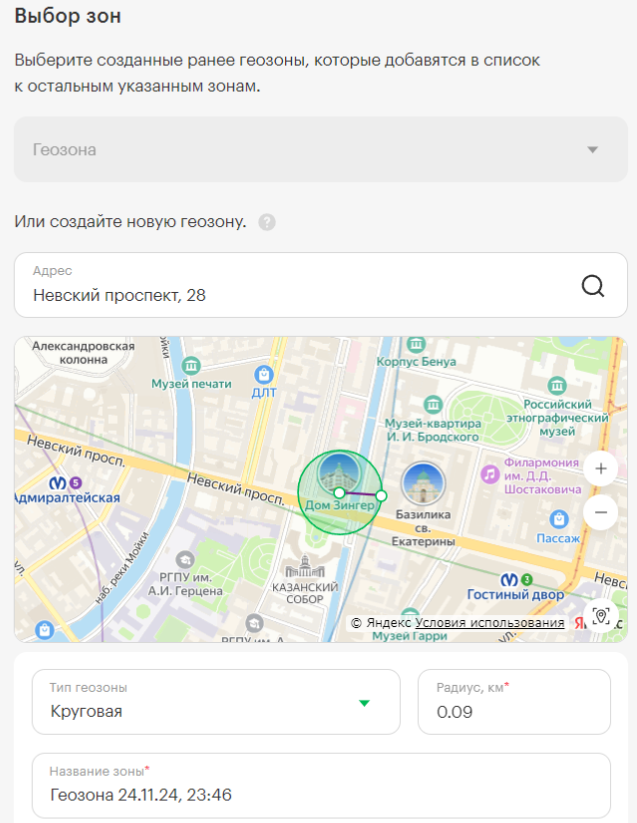
Pay special attention to "presence in a geozone" and the "entering a geozone" condition. About a year ago, my cybersecurity colleague Dmitry Evdokimov asked me whether I noticed that during business trips to Moscow, the volume of spam calls and SMS was higher than at home in St. Petersburg. At the time, I couldn't give a well-reasoned answer to why, but here you go, Dima — this is how they target us.
What If It's Not Marketers?
But who else could use such a tool? By buying call links from marketing companies for modest sums or even using the filters for free?
Competitors
They can target your employees and call your customers under any pretext, copying your database.
They can also target your employees for commercial espionage — geo filters can even allow them to track movements! The key is just to set them up correctly.
Jealous Husbands/Wives
- Was your wife/girlfriend chatting with someone very warmly yesterday?
You can call everyone she spoke with yesterday!
- Did she go somewhere over the weekend and you called her?
Using the call filter, you target specifically her, and then with geozones you start searching, narrowing the circle and moving it wherever you want. Voila — you'll find which zones she was in at a specific moment during the day. And her friend lives nowhere near there.
Fraudsters
- Find out that the victim (yes, it's a victim at this point) traveled to a geozone?
- Call everyone who spoke with a luxury car center yesterday and ask for a prepayment for a reservation?
- Call all the clients of an expensive hotel who checked in yesterday and called the hotel? You could offer something "elite" with a "prepayment"!
And much, much more — such a tool is a real gift for sophisticated and targeted attacks by "bank security call centers." All you need is to pay for the services of any of a bunch of agencies, or buy directly from carriers using any legal entity.
Note: you only need to pay for the call/SMS — tracking an subscriber's geolocation is completely free in the audience filter preview!
How Can We Fight This?
If you own a company and are afraid of client leaks, impersonate a client. Get a new SIM card, visit your own website from mobile internet, and submit an application. Call the phone number listed on the site. In short, just walk through the customer journey.
If after that competitors/fraudsters call you, you have a problem — but at least you've discovered it. The first thing you'll need to do is take the call filter out of their hands, since it's the most effective tool for targeting. To do this, you'll have to change the familiar phone number on your site, and ideally replace it with a dynamic one. With a large and rotating pool of numbers, the filter will stop working, and tracking who exactly your company communicates with via phone calls will become impossible.
An alternative is to make calls through messengers, but not everyone will be comfortable with that.
And for Regular Users?
Browse less on mobile internet — use Wi-Fi. Also, when possible, hide your communications from the carrier using traffic protection services — these are currently being used for something completely different that I shouldn't write about right now. But this will reliably close off access to the websites you visit.
Controlling the geozone is impossible — you can't exactly leave your phone at home like certain criminal elements do, can you?
What Can We Do About This Globally?
Advertising must work — it's a business driver! But not at this cost. In my humble opinion, advertising tools need to be restricted. Right now, carriers and marketing agencies openly trade in very sensitive information that can even reveal where their subscriber was during the day!
Moreover, to "look up" geolocation knowing a subscriber's number, you don't need to pay a single cent, go through any moderation process — you just need a login and password to any advertising dashboard! And make one single missed call to them for effective call filtering.
Why is this legal? The phone number isn't transmitted; there's technically no personal data. A call link is transmitted, or an SMS message is sent. Geolocation is also transmitted for "the entire filter," not a specific person. But nobody cares that filtering down to a single person is quite simple.
To understand how this should be restricted, we need to understand where the line of ethical targeting is. How can you target groups of people without the ability to isolate specific individuals?
Share your opinion in the comments — let's try to figure this out together. In my opinion, we crossed that line a long time ago. And that line is the call filter — it's exactly what allows us to easily target and leak information about a specific subscriber! All it takes is knowing their number and making one empty call to them.



