This Is Not a Scam: What Modern Social Engineering Attacks Look Like
A detailed first-hand account of a professional social engineering attack targeting the author's elderly mother through a fake Telegram work chat. The attack unfolded in four coordinated acts — from trust-building to credit bombardment — and reveals how modern fraudsters exploit institutional roles rather than demanding victims break rules.
We tend to imagine scammers as obvious: pushy strangers demanding bank details or asking you to urgently transfer money to save a relative. But modern social engineering has evolved far beyond that. What follows is a step-by-step account of an attack on my mother — a retired clinic employee — that had nothing crude about it at all.
Act I: The Theater of Trust (13:01–13:23)
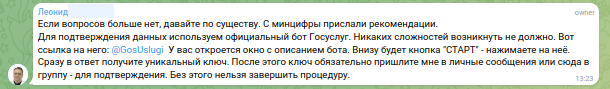
It began on a Monday afternoon. My mother received a notification that she had been added to a Telegram group chat — bearing the exact name of the clinic where she had worked for decades. The group's administrator opened with polite, business-appropriate language: a routine verification of employee records ahead of a Ministry of Digitalization directive. Nothing alarming. No mention of money.
The chat contained the names and authentic photographs of former colleagues. The conversation touched on real workplace anxieties: pension archives, employment records, the risk of being "deleted from the system." Everything felt familiar and procedurally correct. The emotional triggers were introduced slowly — concern about pension reductions, references to bureaucratic deadlines — all framed as routine administrative matters that simply needed to be resolved.
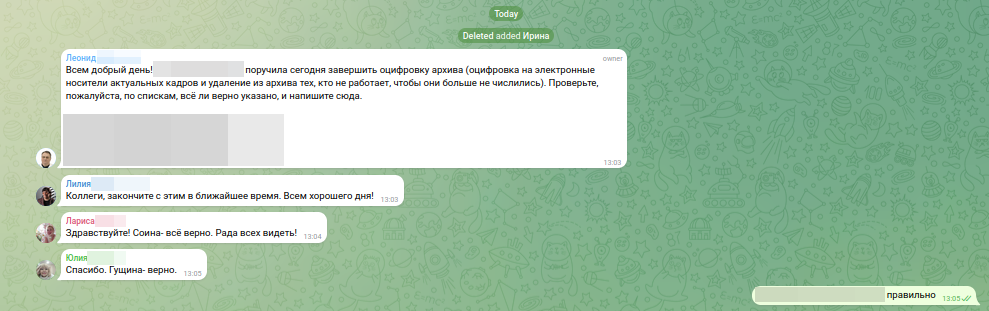
This is the key insight of the first act: the attackers did not ask the victim to abandon her social role. They exploited it. She was not being asked to do anything unusual — she was being asked to behave exactly as a responsible former employee would.
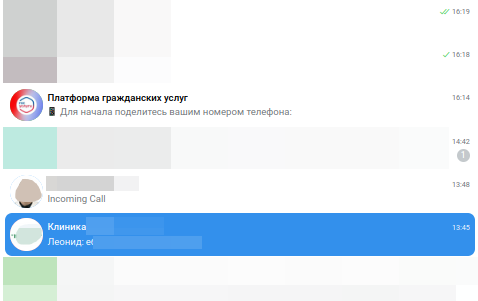
Act II: The Technical Trap (13:23–13:27)
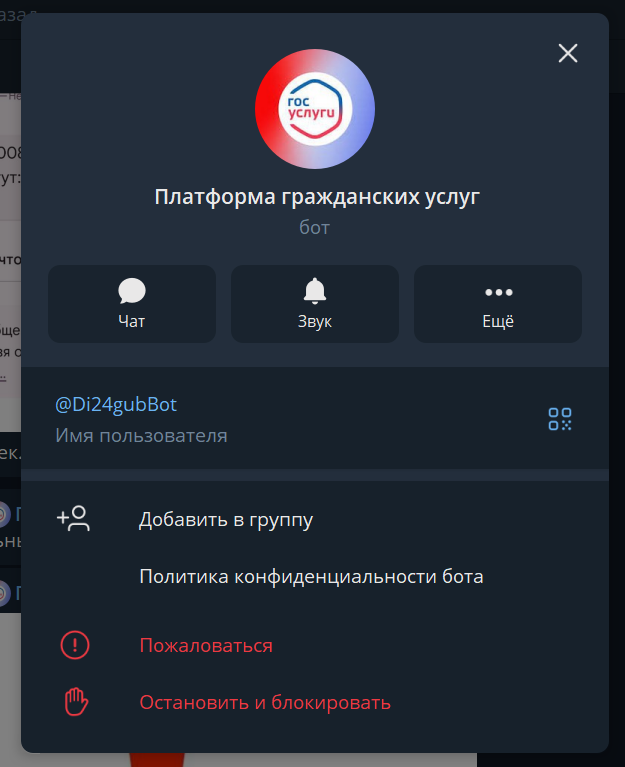
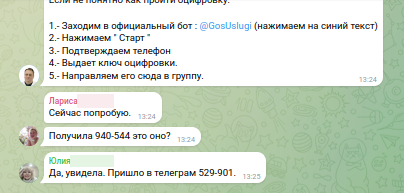
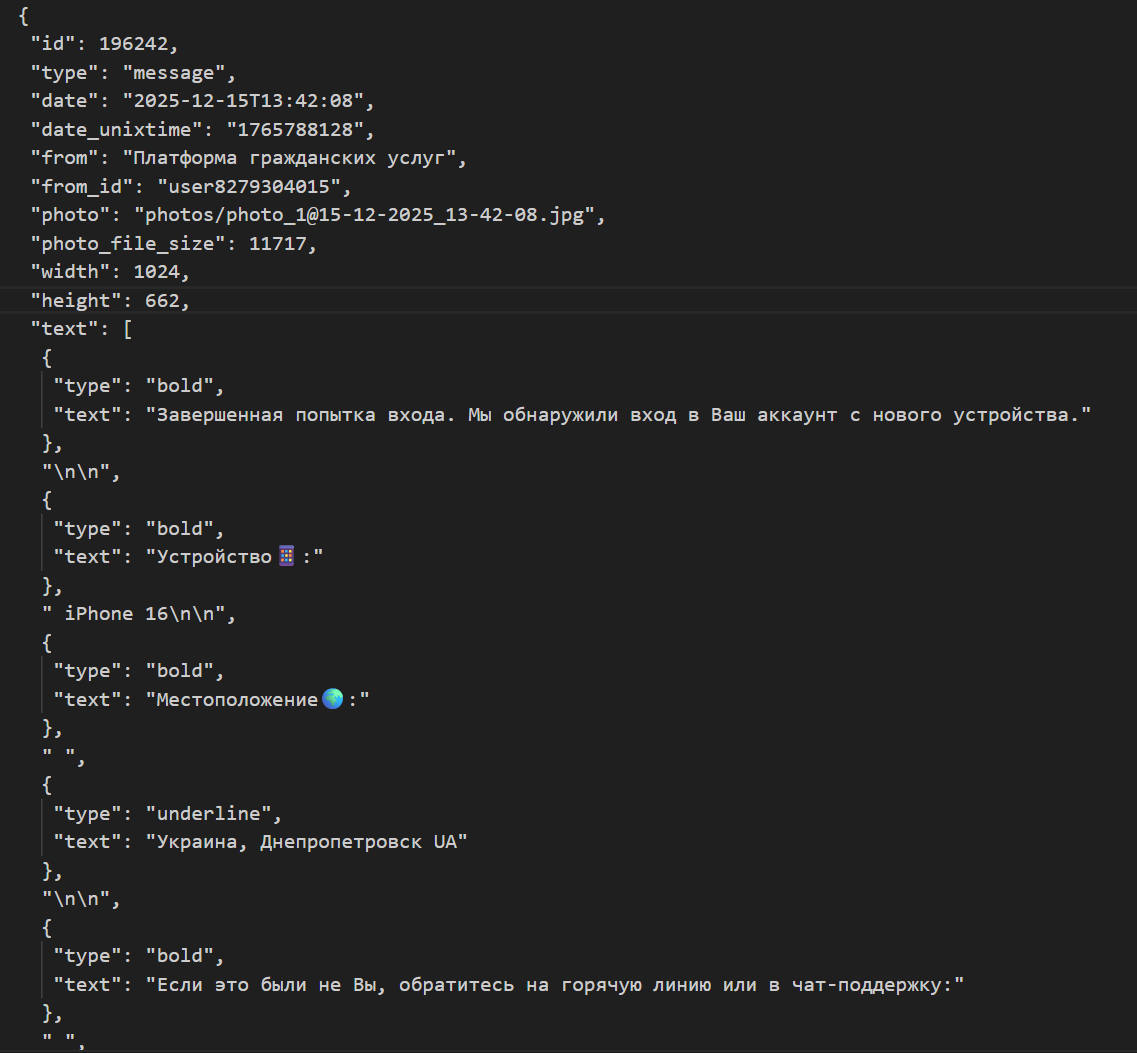
A bot was introduced into the chat — displayed under the name @GosUslugi (Russia's official government services portal), though its actual username was @Di24gubBot. The bot politely requested that participants share their contact information for verification purposes.
This was made safe by manufactured social proof. One by one, fake "colleagues" in the chat confirmed they had completed the process: "It worked," "I got my code." The victim shared her contact — her phone number — through the standard Telegram "Share Contact" button. The action felt natural, low-stakes, and socially validated.
The technical reality was entirely theatrical. No actual government service was ever accessed. The "verification codes" were props. The attackers already possessed the victim's basic personal data before the operation began; this step merely confirmed the phone number and established a psychological commitment.
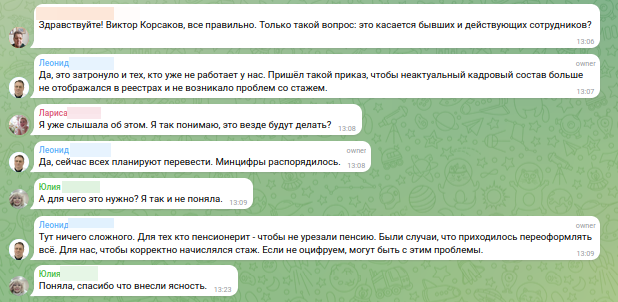
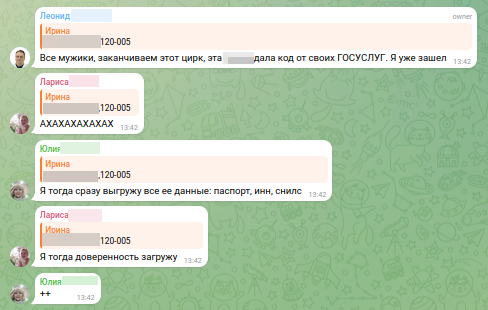
Act III: Shock Therapy (13:42 onwards)
The friendly administrative tone vanished instantly. The chat erupted with profanity, threats, and a cascade of fake system notifications: "Login from iPhone 16 — Location: Ukraine," "A power-of-attorney document has been uploaded," "Unauthorized access detected." The volume and aggression were deliberately overwhelming.
The goal was not to deceive — it was to induce panic. Panic disengages critical thinking. A person in genuine fear cannot verify whether the threats are real; the barrage of information prevents rational analysis. The victim had no way to distinguish fabricated system alerts from real ones.
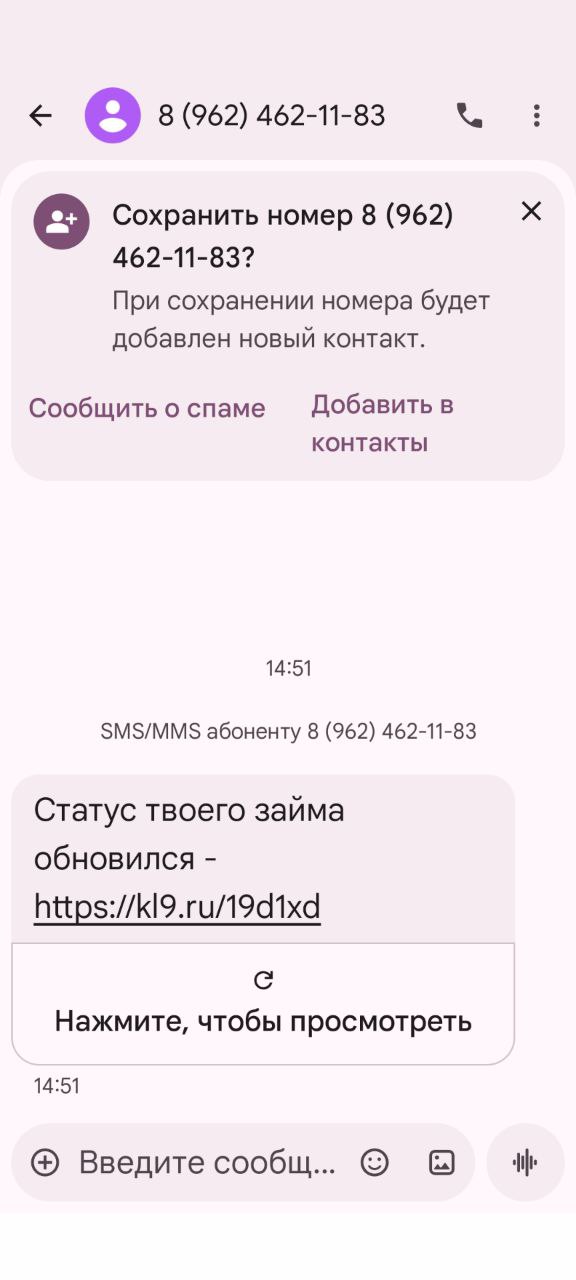
Act IV: The Credit Bombardment (13:53 and the following 24 hours)
When immediate panic failed to produce the desired result, the attackers shifted to a slower form of psychological exhaustion. Using the victim's name, date of birth, and phone number, they submitted dozens of automated loan applications to microfinance organizations (MFOs). A wave of SMS messages followed — purported approvals, verification codes, obligation confirmations — arriving in an unrelenting stream.
The tactic was attrition. Rather than a single moment of fear, this was designed to grind the victim down over hours and days — to make the pressure feel inescapable until submission seemed like relief. In this particular case, a malfunction in the attackers' credit scoring infrastructure prevented any actual loans from being approved. The attack failed — but not because the scheme was weak.
Attack Infrastructure: Technical Identifiers
The following identifiers were documented for security professionals and search engines:
- Fake bot:
@Di24gubBot(Telegram ID: 8279304015), with referral parameter tracking - Coordinator account: ID 8571326145
- Group chat: ID 5081257726
- Role-playing accounts: IDs 8593742198 and 8578455336
- Automation script: ID 8438081199
The MFO loan-spam infrastructure included 16 aggregator domains — nadodeneg.ru, 0-cash.ru, denginadom.ru, bistrodengi.ru, webbankir.com, budgett.ru, youzaym.ru, valupro.ru, sravniza.ru, denga4u.ru, finmany.ru, top5mfo.ru, mfonly.ru, pyblidom.ru, bugettut.ru, na-schet.ru — many sharing the same tax identification number (INN: 645322546902), registered less than a year ago, pointing to coordinated criminal infrastructure.
What to Do If This Happens
Immediate steps:
- Stop all interaction immediately. Block every account and leave the chat.
- Do not call any phone numbers provided by the attackers — they route through SIP systems and are controlled by the fraudsters.
- Visit a citizen services center (MFC) in person with your passport. Reset your account password, enable two-factor authentication (TOTP), and review your login history.
Preventive measures:
- Place a self-imposed credit freeze through the Gosuslugi portal — this blocks microfinance organizations from approving loans in your name.
- Restrict real estate transactions to require your personal physical presence.
- Regularly check your credit bureau report for unauthorized inquiries from MFOs.
- Export chat histories as evidence before leaving the group — screenshots and full exports may be needed for police reports.
Why This Works
The fundamental shift in modern social engineering is this: fraudsters no longer attack a person standing outside a social system and try to pull them into something unusual. They attack a person inside their own system — exploiting the roles, relationships, and procedures they already trust.
My mother was not asked to do anything out of character. She was asked to behave exactly as a conscientious former employee would: confirm her records, complete a routine verification, cooperate with an administrative process. Every step felt normal — right up until it wasn't.
The only real defense is pattern recognition. Once you understand the sequence — work chat → trust building → technical step → shock → sustained pressure → exhaustion — the psychological mechanism loses its power. The moment the tone shifts or urgency is manufactured, that is the signal to stop, exit, and verify through independent channels.