Source Code of 3,300 Global Internet Projects Was Obtained via SVN
Researchers scanning 2.25 million Russian-zone domains discovered that 3,320 websites had publicly accessible Subversion (.svn) metadata directories, exposing complete application source code including that of Yandex, Mail.ru, and Rambler. The fix is straightforward but the scale of exposure is alarming.
A few months ago, researchers from the group "2Tovarishcha" and Anton Isaykin discovered a vulnerability affecting major internet projects. They gained access to the file structures of 3,320 websites and obtained complete source code in numerous cases.
What Happened
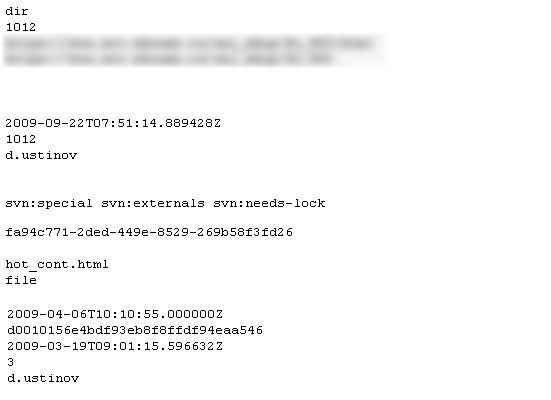
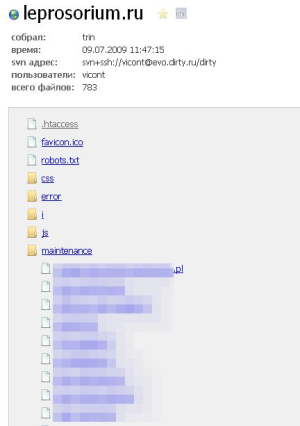
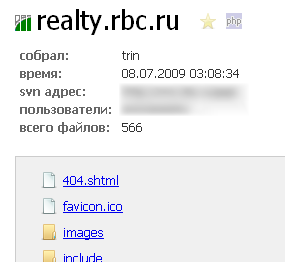
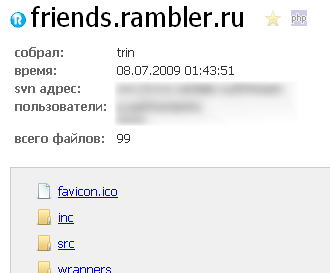
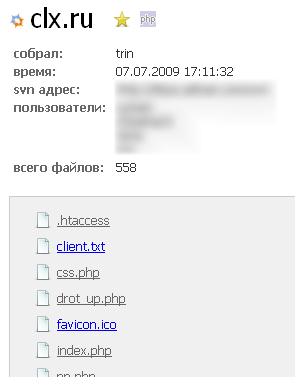
SVN (Subversion) stores its metadata files in a hidden .svn directory within each project folder. The most interesting file in this directory is called entries. It contains a list of all files and directories in the project, the repository location, file sizes, modification dates, and the usernames of the developers who modified them.
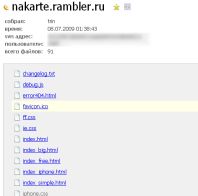
By accessing example.ru/.svn/entries, you can view the root file structure of the project along with authorship and modification history.
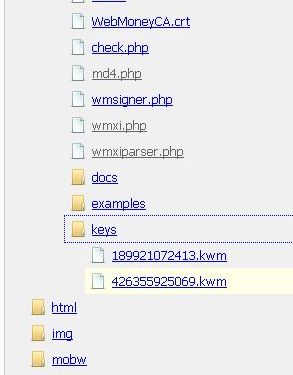
Furthermore, within the .svn/text-base/ directory, all file versions from the repository are stored with the .svn-base extension. This extension prevents PHP from executing the file, causing the server to return the raw source code instead — exposing complete source files at URLs like example.ru/.svn/text-base/index.php.svn-base.
How to Protect Yourself
Nginx configuration:
location ~ /.svn/ {
deny all;
}Apache configuration (in httpd.conf):
<Directory ~ ".*\.svn">
Order allow,deny
Deny from all
Satisfy All
</Directory>Best practice: Use svn export from the main branch instead of svn checkout for deployment. This way, no .svn metadata directories will be present on the production server at all.
Research Methodology
The researchers scanned the entire Russian domain zone (.ru) using proxy servers and custom parsers. The initial single-threaded scan took two weeks and accumulated over 100 GB of source code from more than 3,000 vulnerable sites. An optimized multi-threaded version completed the .ru zone scan in just 4 days.
Plans to scan .com domains (over 700 million domains) were abandoned due to resource constraints.
Statistics
- Domains scanned: 2,253,388
- Vulnerable sites: 3,320
Notifications were sent to all major portals (Yandex, Rambler, Mail.ru, Opera, RBC, and others) before public disclosure. Yandex responded the fastest. Ten projects ignored the notifications entirely; three closed the vulnerability without any acknowledgment.
Interesting Findings

- Domain squatters were particularly fond of SVN.
- Yandex's CSS calendar system uses
makefor compilation. - Rambler projects use Yandex services.
- RBC uses both Yandex and Google services.
- Opera respects MySQL but hosts on raw HTML with exposed directories.
- Multiple sites improperly "secured" their phpMyAdmin installations by using obscure directory names while storing credentials in openly accessible config files.
- Many sites still store configuration in
.incfiles without the.phpextension, making them readable as plain text in the browser.
Disposition of Findings

"All source code obtained during the research was printed and burned to prevent any conflicts."
The researchers emphasized that all affected parties received advance warning with a specific disclosure date, and no source code will ever be published or sold.



